Transaction Signing
Overview
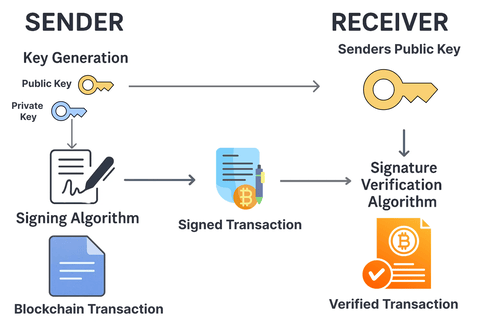
Transaction signing is a basic process in blockchain systems to verify the ownership and validity of a transaction so that only authorized parties can initiate or authorize transfers of digital assets. Transactions would be open to fraud, unauthorized access or tampering without a valid cryptographic signature, risking the security and trust in the blockchain.
MPC Transaction Signing
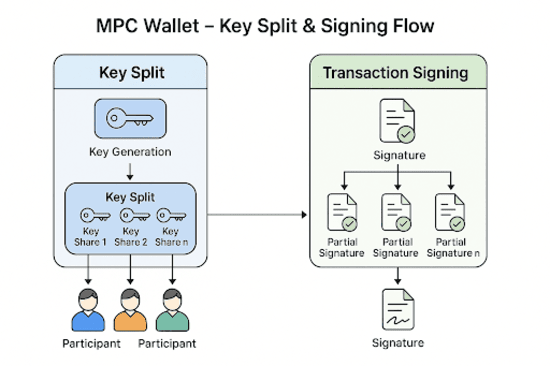
Multi-Party Computation (MPC) wallets enhance this process by enabling decentralized, secure, and private transaction signing. Unlike their single private key competitors, MPC wallets distribute the key into secret shares across different participants or devices, with the following benefits:
-
Enhanced Security: The private key is never stored in one place or reconstructed. Participants safely construct an authentic signature (e.g., ECDSA) without exposing their shares, reducing the threat of key theft or loss.
-
Privacy through Zero-Knowledge: MPC prevents any participant from learning others' secret shares during signing, keeping confidentiality and avoiding misuse.
-
Threshold-Based Authorization: There should be a pre-defined threshold (e.g., t+1 of n participants) that must sign, providing fault tolerance against individual failures or attacks while maintaining operational flexibility.
-
Blockchain Compatibility: MPC wallets provide standard cryptographic signatures required by blockchain networks like Bitcoin or Ethereum, allowing secure and auditable transactions.
-
Resistance to Attacks: Because the key is distributed among multiple participants, MPC wallets dampen the impact of a single attacked participant, thus enhancing overall security.
Briefly, MPC wallet transaction signing offers secure, private, and fault-tolerant approval of blockchain transactions without the need for a centralized private key. MPC wallets are thus optimized for high-security applications, such as institutional custody or multi-user crypto management.
Algorithms for Transaction Signing
Numerous algorithms are used for transaction signing across different blockchains. However, not all blockchains rely on the same signature schemes, which can lead to compatibility issues. In this section, we introduce several signature algorithms that offer distinct advantages in terms of security, efficiency, and suitability for Multi-Party Computation (MPC) environments. While these algorithms are not universally compatible with all blockchains, they provide strong foundations for secure and collaborative signing protocols:
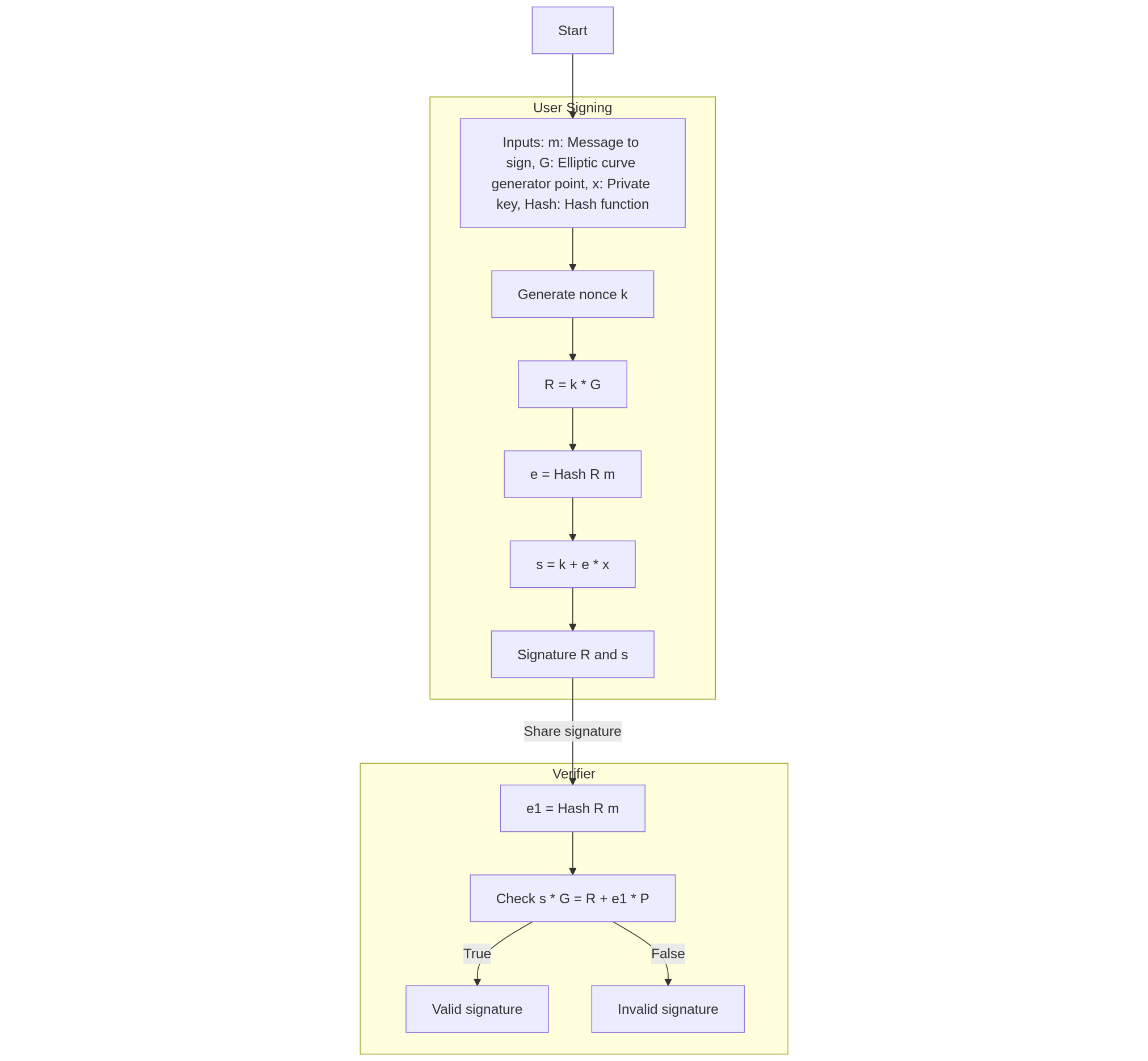
1. Schnorr Signature
The Schnorr signature algorithm is a cryptographic method for signing messages. The Schnorr signature scheme is not threshold-based in its original form, but its mathematical structure makes it an ideal foundation for designing threshold signatures and multisignature (multisig) schemes. It is renowned for its ability to generate short, compact signatures quickly, making it efficient for a variety of applications. Schnorr signatures employ elliptic curve cryptography to provide high security with lower computational complexity. For a detailed explanation of the algorithm, refer to Wikipedia: Schnorr Signature and Crypto StackExchange: EC-Schnorr Multiple Standards. It is high-performance and simple and is a fundamental building block for more advanced signing schemes.
Algorithm
Assume the private key and public key are already generated, with an elliptic curve defined by a generator of order , and a hash function (e.g., SHA-256).
Signing
For a message and private key , the nonce must be random and unique for each signature to prevent private key exposure:
Sign:
- // Generate a random nonce
- // Compute point on the elliptic curve
- // Hash of and message
- // Compute
- return // Signature is the pair
Verification
For a message , signature , and public key :
Verify:
- // Hash of and message
- If , return True // Signature is valid
- Else, return False // Signature is invalid
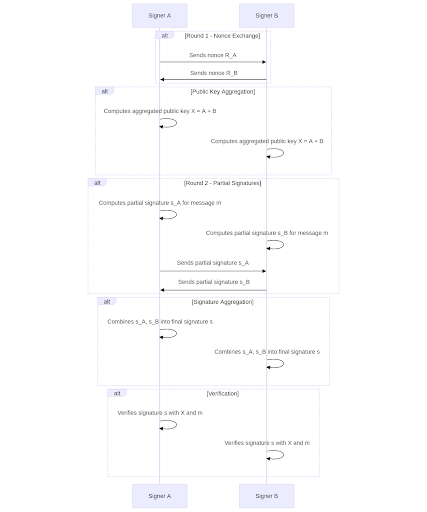
2. MuSig2 (Simple Two-Round Schnorr Multi-Signatures)
MuSig2 is an advanced multi-signature scheme derived from the Schnorr signature system. It is the successor to MuSig1, which enabled multiple parties to collaboratively sign a message by aggregating their individual keys into a single public key and producing a single aggregate signature for a specific transaction. This aggregation reduces data size, lowers associated costs, and enhances privacy by concealing individual signer identities. MuSig2 simplifies the previous scheme by requiring only two rounds of communication among participants to produce a valid signature, making coordination easier and reducing complexity compared to MuSig1’s three-round protocol. For a detailed explanation of the algorithm, refer to https://eprint.iacr.org/2020/1261. This makes it particularly well-suited for distributed signing scenarios.
Algorithm
Assumptions:
-
An elliptic curve with a generator of order .
-
A hash function (e.g. SHA-256).
-
A group of signers, where each signer has:
- Private key
- Public key
-
A message that all signers wish to sign.
-
The aggregated public key is computed as , where are key aggregation coefficients (e.g., ).
-
Each signer generates two nonces (or more, depending on configuration, but we describe the variant with ).
Steps:
MuSig2 consists of two communication rounds, where the first round can be preprocessed before the message is known, enabling nearly non-interactive signing.
-
First Round: Nonce Sharing
1.1. Nonce Generation:
-
Each signer generates two random nonces .
-
Computes the corresponding elliptic curve points:
1.2. Nonce Sharing:
-
Each signer sends their nonce points to the other signers (via a secure channel).
-
This round can be performed in advance, before the message is known.
-
-
Second Round: Signing
2.1. Prepare Aggregated Values:
-
All signers receive the nonce points from others.
-
Compute a hash coefficient: , used for linear combination of nonces.
-
For each signer , compute the aggregated nonce point:
-
The total nonce point is:
2.2. Compute Message Hash:
- Compute , where is the aggregated public key.
2.3. Generate Partial Signature:
- Each signer computes their partial signature:
- Signer sends to the other signers.
2.4. Aggregate Signature:
- All partial signatures are summed:
- The final signature is the pair .
-
Verification
Verification of a MuSig2 signature is identical to standard Schnorr verification.
For message , signature , and aggregated public key :
- Compute:
- Check if:
- If the equality holds, the signature is valid; otherwise, it is invalid.
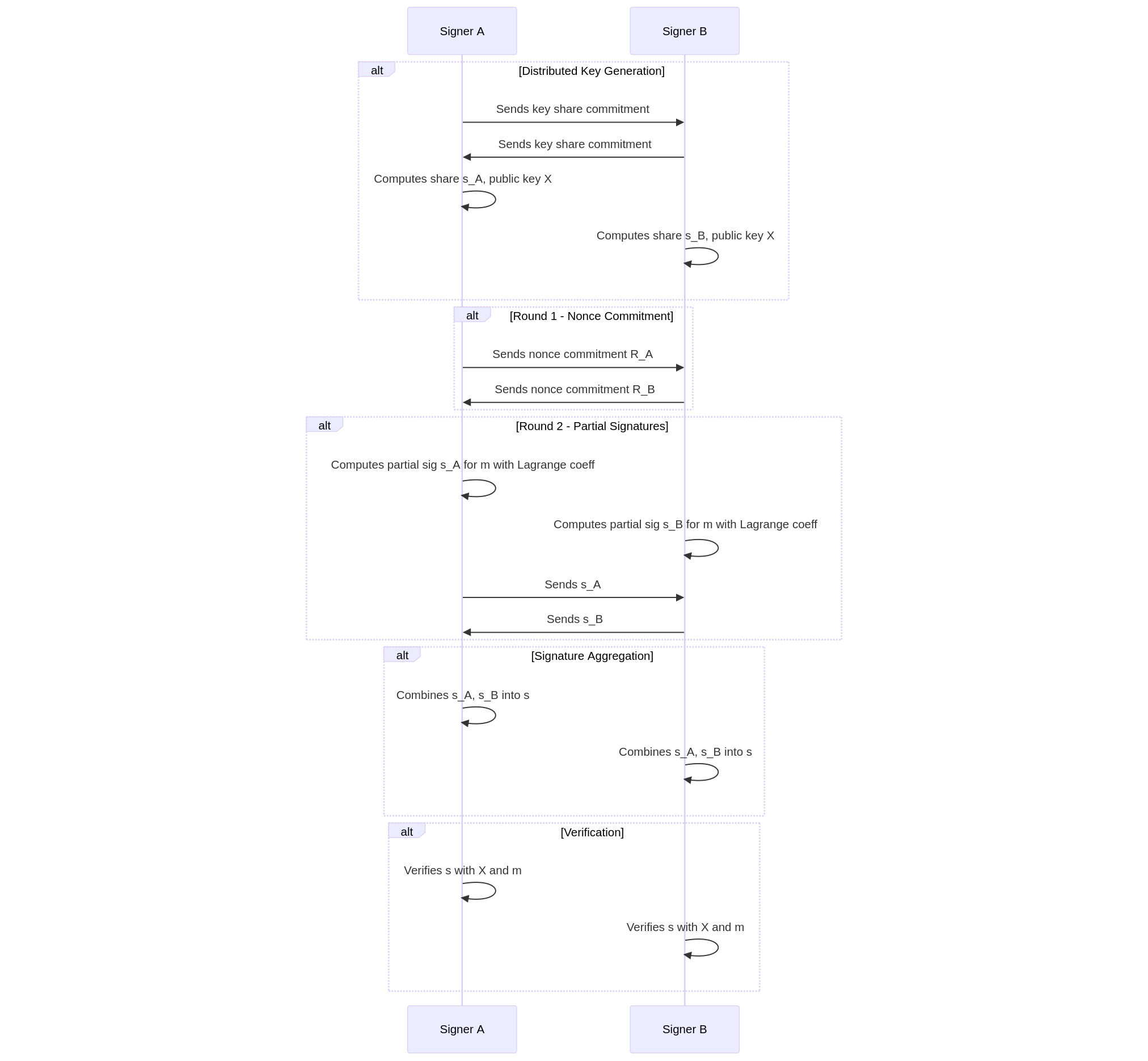
3. FROST (Flexible Round-Optimized Schnorr Threshold Signatures)
FROST is a Schnorr-based threshold signature scheme which achieves flexibility in the signing process. Depending on the application, it supports single-round and two-round signing protocols. The minimum number of signers needed (e.g., 3 of 5) is set as the threshold, which allows partial participation without sacrificing security. FROST provides mechanisms to deal with critical signers; if a participant fails or acts maliciously, the protocol can abort the participation of the party and proceed without it. This adds flexibility in dynamic environments. An example implementation of FROST is available at University of Waterloo Git: FROST, which is a useful reference for its implementation.
Algorithm
Initialization (Distributed Key Generation - DKG)
Goal: Generate a shared public key and distribute secret shares of the private key among participants.
-
System Parameters
- Define cryptographic parameters: an elliptic curve, a generator point , and the group order .
- Set the threshold (minimum number of participants needed for signing) and the total number of participants (where ).
-
Polynomial Generation
-
Each participant (for ) chooses a random polynomial of degree where the constant term is their secret key .
-
The polynomial is:
with random coefficients in .
-
-
Commitment Sharing
-
Each participant computes public commitments for their polynomial coefficients:
-
These commitments are shared with all participants to enable verification.
-
-
Secret Share Distribution
-
Each participant computes a secret share for every other participant :
-
These shares are sent to participant over a secure channel.
-
-
Verification and Aggregation
-
Each participant verifies the received shares using the commitments .
-
If valid, each participant computes their private key share:
-
The shared public key is:
-
Result: Each participant holds a private key share , and the group has a shared public key .
Signing (Two-Round Signing)
Goal: Generate a valid Schnorr signature for a message using at least participants.
-
First Round: Nonce Generation
-
Each participant selects two random scalars .
-
They compute two commitments:
-
The nonce commitments are sent to all participants.
-
-
Nonce Aggregation
-
A coordinator (or each participant) collects the nonces and computes the aggregated nonce:
-
Where:
- is the set of participants.
- is a hash specific to the message and participant (e.g., ).
-
-
Second Round: Partial Signature Generation
-
Each participant computes the challenge:
-
They generate a partial signature:
-
Where is the Lagrange coefficient for interpolation at point .
-
Each participant sends to the coordinator.
-
-
Signature Aggregation
-
The coordinator verifies the partial signatures and aggregates them:
-
The final signature is the pair .
-
-
Signature Verification
- The signature is verified using standard Schnorr verification , where
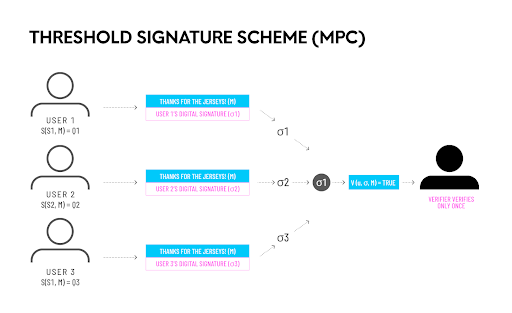
Threshold Signature Schemes (TSS)
Threshold Signature Schemes (TSS) are an excellent match for MPC wallets. TSS enables the creation of different combinations of distributed key shares that all together amount to the equivalent of the same private key, without needing to re-create the private key when adding or removing participants or thresholds. This flexibility also allows adding new members to a pre-existing key without altering existing users' private keys, making group management easier. Signing occurs off-chain, with a minimum of data being sent to the blockchain, which accelerates transaction execution and lowers costs. TSS is highly adaptable, allowing for the modification of various underlying algorithms (e.g., Schnorr-based schemes) for threshold signing, making it an agile solution for MPC applications.
Algorithm
Assumptions
- There are participants, with required to sign.
- The private key is split into shares using Shamir Secret Sharing.
- The public key is known to all (where is the elliptic curve generator).
- The message to sign is with its hash .
- The elliptic curve has parameters: (group order), (generator).
Steps of the Algorithm
-
Initialization
- Each participant holds their private key share .
- Participants agree on a random nonce using a distributed key generation protocol (e.g., Pedersen DKG).
-
Nonce Generation
-
Each participant generates their nonce share (split via Shamir Secret Sharing).
-
Participants jointly compute using their shares without revealing .
-
Compute:
where is the -coordinate of point .
-
-
Signature Computation
-
Each participant computes their signature share :
where is the modular inverse of .
-
A subset of participants combine their shares using Lagrange interpolation (in field ) to obtain the final :
where are the Lagrange coefficients.
-
The final signature is the pair .
-
-
Signature Verification
Verification follows the standard ECDSA procedure:
-
Compute:
-
Compute:
-
Check if:
-
If true, the signature is valid.
-
TSS based on ECDSA
The efficiency of different TSS implementations depends greatly on the underlying signature algorithm. For example, Schnorr-based signature schemes offer a simpler and more efficient solution for TSS compared to ECDSA-based TSS, due to the linear and additive nature of Schnorr signatures, which makes secure distribution and aggregation easier. Although Schnorr-based signatures are more TSS-friendly, ECDSA-based TSS is more commonly used because ECDSA is widely adopted in existing systems, wallets, and platforms like Bitcoin and Ethereum, ensuring compatibility. Despite being more complex, ECDSA preserves interoperability with established cryptographic infrastructure.
For the above-mentioned reasons, significant research efforts have been devoted to improving the efficiency of ECDSA-based TSS. Zero-knowledge proofs (ZKPs) enable one to verify the validity of a statement without revealing the underlying data, a feature that has become increasingly significant for cryptographic protocols such as threshold signature schemes (TSS). While such algorithms can enhance the security of TSS, they are often computationally demanding, which can impact the overall efficiency of these systems. The MacKenzie-Reiter algorithm, an early TSS solution, utilized zero-knowledge proofs heavily in the Distributed Key Generation (DKG) process. Due to its computational heaviness and resource demand it failed to keep up with the pace of practical engineering demands. Recent advancements in ZKP technology have spurred the development of more efficient TSS algorithms, which are being utilized heavily in multi-signature wallet solutions in the blockchain ecosystem. One of these algorithms is Lindell's 2017 protocol, which optimized the MacKenzie–Reiter protocol by minimizing the complexity of ZKP proofs. Below, we outline the top TSS algorithms based on the Elliptic Curve Digital Signature Algorithm (ECDSA).
1. Lindell17
The Lindell17 protocol, eprint.iacr.org/2017/552.pdf, is a two-party TSS protocol designed for ECDSA. It significantly improves the efficiency of MacKenzie–Reiter by optimizing cryptographic proofs and interactions. One of the implementation examples is the Gotham City project by ZenGo-X.
-
Mechanism: Lindell17 employs homomorphic encryption, the Paillier cryptosystem, to calculate an ECDSA signature. It adopts a client-server model in which both entities hold a share of the private key. The signature is finalized by one of the two entities, generally the server.
-
Properties: The protocol is two-party fast signing optimized, with Paillier encryption used to securely compute the signature without fully reconstructing the private key.
-
Vulnerabilities: Vulnerabilities were discovered by Fireblocks in certain open-source implementations (e.g., ZenGo and Coinbase WaaS) that deviate from the scientific paper.
Algorithm
-
Setup & Key Generation (Offline)
1.1. Participants in the protocol, and , generate random numbers and , respectively, which represent their secret key shares.
1.2. computes and computes .
1.3. and exchange Pedersen commitments for shares.
1.4. Participants prove in zero-knowledge that exchanged commitments contain valid discrete logarithms.
1.5. One participant generates a Paillier keypair and proves in zero-knowledge its correctness to the other participant.
1.6. Both parties compute the public key and verify proofs.
Result: Both participants hold additive shares of the private key and the common public key .
- Online Signing (2 rounds)
When signing a message :
- Round 1: Share Randomness
- Both participants generate random shares and nonce shares , keeping them secret.
- Participants exchange Pedersen commitments of these shares along with zero-knowledge proofs to validate correctness.
- Round 2: Computations
- Both parties compute in the same way is computed in the first part, and extract as the -coordinate of point .
- Based on and (where ), parties compute by using homomorphic encryption and modular arithmetic to securely multiply shared secrets without revealing them.
- Similarly, they compute using the shared values and homomorphic methods.
- Parties reveal the (homomorphically computed) values and ; both agree on the results.
- Both parties calculate which provides them with a valid ECDSA signature .
2. GG18
GG18 protocol https://eprint.iacr.org/2019/114.pdf, suggested by Gennaro and Goldfeder, is DSA and ECDSA compatible and is a simple multi-party TSS with zero-knowledge extensions.
-
Mechanism: GG18 uses four rounds in the DKG phase: three for sharing keys and one for public key verification. Nine rounds are required for signing, with two Multiplicative-to-Additive (MtA) procedures between each pair of participants. These MtA steps, secured with zero-knowledge proofs, convert multiplicative shares to additive ones for ECDSA computation.
-
Properties: While viable for any threshold (t, n), the high round complexity of GG18 (nine rounds for signing) is computationally costly. The protocol halts when a malicious participant is detected, but it cannot identify the misbehaving party, which limits accountability.
-
Use Case: Its security strength is suitable for use cases requiring strong security, albeit at the cost of its efficiency.
Algorithm
1. Key Generation Phase (Distributed Key Generation - DKG)
-
Initialization
- A group of participants aims to generate a shared public key and distributed shares of a private key.
- A threshold is defined, where at least participants are needed to reconstruct the secret, but fewer than learn nothing (zero-knowledge property).
- A cryptographic system is used, typically based on elliptic curves or similar structures.
-
Polynomial Generation
- Each participant (for ) randomly generates a secret polynomial of degree
- The polynomial is of the form , where is the participant’s secret, and coefficients are randomly chosen from a finite field.
-
Commitment
- Each participant computes Pedersen commitments for the coefficients of their polynomial , where is a group generator (e.g., on elliptic curves).
- These commitments are publicly broadcast to ensure verifiability and prevent later changes.
-
Sharing Secret Values
- Each participant computes secret shares for every other participant , where is the index of another participant.
- These shares are sent privately (e.g., encrypted) to participant .
-
Verification of Shares
- Each participant receives secret shares from others and verifies them using the commitments .
- Verification is done via the equation
- If verification fails, participant can complain against for sending invalid shares.
-
Handling Complaints
- If complaints arise, the system identifies misbehaving participants.
- Participants who send invalid shares are disqualified, and the process continues with remaining participants.
- Continuation requires a mutual informal agreement, a sufficient number of honest parties, and trust that all honest parties share the same view of the group.
- Note: This method does not provide cryptographic proof of misbehavior.
-
Computing Final Shares
- Each participant sums all valid shares received:
- This becomes the secret share of the private key for participant .
-
Generating the Public Key
- The shared public key is computed as: is the secret private key (which no single participant knows).
- The public key can be derived using commitments: since .
-
Zero-Knowledge Property
- No single participant knows the full private key .
- The secret is distributed so that participants are needed to reconstruct it (e.g., via Lagrange interpolation), but fewer reveal nothing (zero-knowledge).
2. Signing Protocol (Threshold ECDSA)
Goal: Given the shared private key (from Part 1, DKG) and the message hash , a threshold parties (out of ) can compute a valid ECDSA signature:
The core challenge is to compute without revealing the secret shared key and the shared nonce .
To do this securely, GG18 uses:
- Paillier homomorphic encryption (for secure multiparty multiplication).
- Multiplicative-to-additive (MtA) protocol.
- Zero-knowledge proofs (for security against malicious behavior).
Signing Steps (GG18):
-
Each party samples a random , computes and publishes to others. Then everyone computes the public nonce point and the -coordinate of becomes All parties agree on .
-
Each party generates a Paillier encryption keypair and publicly shares . Paillier enables homomorphic addition/multiplication over encrypted data used for secure computation of .
-
Run the Multiplicative-to-Additive (MtA) Protocol. Each pair engages in a two-party MtA protocol to securely compute partial products without learning each other's secrets. The procedure:
- encrypts its secret under ’s Paillier public key
- homomorphically computes
- sends the ciphertext and a zero-knowledge proof of correctness to .
- decrypts and obtains a share of .
This repeats for all pairs; all parties combine results to get Thus, additive shares of numerator are distributed.
-
Each party holding additive shares of and partials from MtA, inverts collaboratively (e.g., with precomputed inverses or MPC) and computes their share After combining shares the final signature is obtained.
-
Each party checks if and . If so, is a valid ECDSA signature under the public key.
3. GG20
GG20 https://eprint.iacr.org/2020/540.pdf, which succeeds GG18, streamlines the process with greater efficiency and accountability. Implementations are available at Safeheron/multi-party-sig-cpp, ZenGo-X/multi-party-ecdsa, and Thorchain/tss-lib.
-
Mechanism: GG20 signing requires seven rounds, where the first six rounds are message-independent and thus preprocessable. It is the same as GG18 in that it uses Paillier encryption and zero-knowledge proofs for MtA operations to provide secure share computation. GG20 is different from GG18 in that GG20 has an identifiable abort mechanism, i.e., it can determine a cheating participant when the protocol aborts.
-
Properties: Seven-round reduction and the ability to preprocess six of them enhance efficiency, while the abortable identification thwarts continued malicious behavior, e.g., denial-of-service-like attacks. This makes GG20 better suited for real-world multi-signature wallet deployments.
-
Improvements: Introduced in 2020, GG20 addresses GG18 weaknesses by reducing round complexity and adding fault attribution, leveraging zero-knowledge proofs for privacy and security in the signing process.
Algorithm
1. Key Generation Phase (Distributed Key Generation - DKG)
The key generation phase of GG20 is largely the same as in the GG18 protocol; therefore, we will present only the additions introduced by the GG20 protocol to the key generation phase described in the GG18 section.
-
Initialization
GG20 enhances the corresponding step in GG18 by introducing session ID binding, each DKG instance is tied to a unique session identifier to prevent replay attacks. Additionally, GG20 uses domain separation tags in hashing to clearly distinguish between different protocol phases. -
Commitment
GG20 adds optional range proofs on commitments to the corresponding step in GG18, ensuring that the coefficients are within the expected size for field soundness. -
Sharing Secret Values
GG20 improves on GG18 by adding encryption of shares (e.g., via Paillier or ElGamal) to ensure confidentiality, and by requiring a zero-knowledge proof that each party’s Paillier modulus N=p⋅q was generated correctly using safe primes preventing trapdoor attacks that GG18 did not guard against. -
Handling complaints
In this step, GG18 does not provide a formal mechanism to prove misbehavior. GG20 introduces Identifiable Abort, which allows a recipient of an invalid share or message to generate a zero-knowledge transcript proving that the sender misbehaved. This non-interactive dispute resolution mechanism enables malicious parties to be identified and excluded from the group, allowing the protocol to proceed with the remaining honest participants.
2: Signing Protocol (Threshold ECDSA)
Step 1: In GG20’s MPC protocol, nonce generation is similar to GG18 but strengthened with robust zero-knowledge proofs that bind each nonce to its corresponding , preventing rogue-key and bias attacks. Additionally, GG20 employs commitments and ZKPs to prove knowledge of discrete logs without revealing , sometimes using augmented proofs to ensure non-malleability and stronger soundness.
Step 2: GG20 retains a similar Paillier key generation process but introduces more efficient, modular zero-knowledge proofs for correct key generation, often leveraging improved, non-interactive proof systems, like those based on the Fiat-Shamir transform, to reduce proof size and complexity.
Step 3: GG20 retains the core MtA concept but enhances it with stronger composable zero-knowledge proofs often using bulletproofs or aggregated proofs to ensure correctness and reduce overhead when proving many operations simultaneously. It also introduces formal guarantees against leakage and malleability, explicit noise binding to prevent replay attacks, and a modular design that makes MtA a standalone, securely composable sub-protocol.
Step 4: GG20 enhances the collaborative inversion step by using a more robust MPC subprotocol with explicit zero-knowledge proofs that each partial signature is consistent with secret shares, preventing rogue key and substitution attacks. It also improves synchronization and state management to ensure protocol compliance and often includes abort-resilient mechanisms to tolerate misbehaving parties below the threshold.
Step 5: GG20 maintains the same final signature validation but adds collective verification steps, including proofs that the signature was honestly computed, and often uses post-signature zero-knowledge proofs to prevent manipulation during share combining. It also optionally provides non-interactive proofs to enable third-party verification of the signature’s validity under the distributed key.
Summary
A variety of protocols exist for transaction signing, each offering different trade-offs in efficiency, scalability, and security. Schnorr signatures provide a minimal single-party baseline, while MuSig2 enhances coordination among multiple parties. FROST, a modern Threshold Signature Scheme (TSS), offers flexible threshold capabilities and efficient signing. More broadly, TSS protocols integrate well with MPC wallets to enable distributed and cost-effective signing. Lindell17, GG18, and GG20 demonstrate the evolution of zero-knowledge techniques in ECDSA-based threshold schemes. Lindell17 is the most efficient two-party solution with fast signing but must be carefully implemented to avoid vulnerability. GG18 provides a secure multiparty computation protocol at the expense of efficiency, and GG20 achieves a trade-off between security, efficiency, and accountability, which is a more desirable protocol for modern blockchain multi-signature wallets. The final choice for the CryptoProcessor project will depend on specific requirements, including the desired threshold, communication constraints, and blockchain integration needs.